Torzon Market Mirror Directory & Verification
PGP-Authenticated Onion Addresses with Real-Time Monitoring

All Verified Torzon Market Mirrors
The following mirror addresses have been cryptographically verified against the official Torzon Market PGP public key. Each mirror connects to the same backend infrastructure, so your account credentials, order history, wallet balance, and encrypted messages remain fully synchronized across every address. Bookmark at least two or three mirrors from this list to guarantee uninterrupted access if a single endpoint experiences temporary downtime. All mirrors listed below use the V3 onion protocol, providing 56-character addresses with the strongest available cryptographic authentication on the Tor network.

Last updated: April 14, 2026 | All mirrors verified active | Total mirrors: 5
How to Verify Mirror Authenticity on Torzon Market
Phishing mirrors are the single greatest threat facing darknet market users today. Attackers clone the entire Torzon Market interface pixel-for-pixel, swap out the backend with credential-harvesting code, and distribute fake links across forums and messaging channels. The only reliable defense is independent cryptographic verification of every mirror before you enter any credentials. The four-step process below ensures you are connecting to an authentic Torzon Market endpoint rather than an impersonation designed to steal your login, PGP keys, or cryptocurrency.
Check PGP Signatures
Download the signed mirror list from this portal and verify its PGP signature using GnuPG. Run gpg --verify Torzon Market-mirrors.txt.asc and confirm the signature matches the official Torzon Market public key. If verification fails or the signing key is unrecognized, do not proceed with any mirror on that list. PGP signature verification is the gold standard for authenticity because an attacker cannot forge a valid signature without possessing the private key held exclusively by the Torzon Market administration team.
Verify Warrant Canary
After loading any mirror, navigate to the warrant canary page before entering credentials. The canary must be updated within the last 72 hours and should reference recent, verifiable news events to prove its creation date. A missing, outdated, or unsigned canary indicates potential compromise of that mirror endpoint. Log out immediately and switch to a different verified address from this directory. The warrant canary system provides an early-warning mechanism that the Torzon Market team has never been compelled to remove, giving users confidence in ongoing operational integrity.
Compare URL Characters
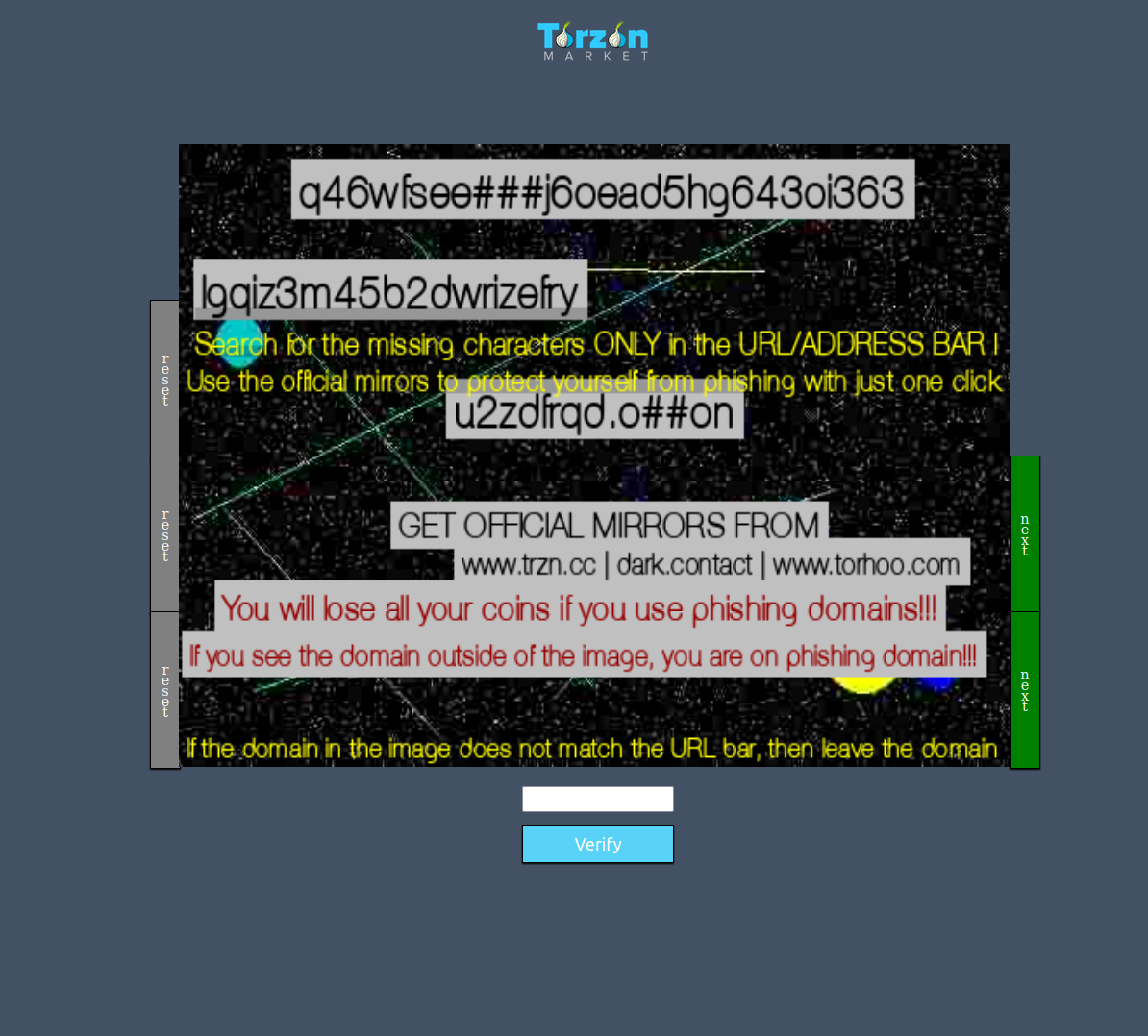
Phishing operators register onion addresses that visually resemble legitimate mirrors by substituting characters such as replacing lowercase L with the digit 1, or the letter O with zero. Always compare the full 56-character V3 address in your Tor Browser address bar against the mirrors listed on this page, character by character. Copy the address from this portal and paste it directly into Tor Browser rather than clicking links from forums, direct messages, or clearnet search results. Even a single mismatched character means you are on a fraudulent endpoint.
Test Mirror Functionality
Authentic Torzon Market mirrors provide full platform functionality immediately upon connection. Test the mirror by browsing public-facing pages, checking that all navigation elements load correctly, and verifying that the CAPTCHA system functions as expected. Phishing clones often have broken elements, missing images, non-functional search features, or redirect you to a simplified login page that skips the CAPTCHA entirely. If the mirror feels incomplete, loads unusually fast, or skips expected security challenges, treat it as suspicious and switch to a different verified address.
Torzon Market: Mirror Infrastructure & Architecture
The Torzon Market mirror network is engineered from the ground up for maximum resilience, geographic diversity, and zero single points of failure. Each mirror operates on independent hosting infrastructure across different jurisdictions, connected through encrypted synchronization channels that keep user data and platform state consistent in real time. This distributed architecture ensures that taking down any individual mirror has no impact on overall platform availability or data integrity.

DDoS Protection
Torzon deploys multi-layer DDoS mitigation across the entire mirror fleet, combining advanced traffic analysis, rate limiting, proof-of-work challenges, and automatic traffic rerouting. When volumetric attacks target a specific mirror, incoming connections are uninterruptedly redirected to healthy nodes within seconds. This layered defense has sustained 99.7% uptime throughout 2024 and 2026, even during coordinated attack campaigns that simultaneously disabled competing darknet platforms for days at a time.
Geographic Distribution
Mirrors are strategically distributed across multiple continents and independent network providers to minimize latency for the global user base and eliminate regional failure risks. A European user connecting to a nearby mirror experiences noticeably faster page loads compared to routing through a distant server. Geographic diversity also protects against jurisdiction-specific takedown actions, internet censorship events, and undersea cable disruptions that can isolate entire regions from the Tor network.
Load Balancing
Intelligent load distribution across the mirror fleet prevents any single server from becoming a bottleneck during peak traffic periods. Torzon Market monitors CPU utilization, memory pressure, and connection queue depth in real time, dynamically shifting new connections toward less-loaded mirrors. This ensures consistent response times for all users regardless of overall platform traffic volume. Maintenance windows on individual mirrors proceed without downtime because the balancer automatically excludes nodes undergoing updates.
Server Seizure Resilience
Every Torzon Market mirror runs entirely from volatile RAM with zero persistent storage on disk. If law enforcement physically seizes a server, the hardware contains no recoverable user data, transaction logs, or encryption keys because all information evaporates the instant power is interrupted. The remaining mirrors continue operating without interruption, and the administration team deploys replacement nodes within hours. This RAM-only architecture represents the highest standard of operational security for darknet infrastructure.
Understanding V3 Onion Addresses on Torzon Market
Every Torzon Market mirror uses the modern V3 onion service protocol, identifiable by its 56-character address format ending in .onion. Understanding how these addresses work helps users appreciate the layers of cryptographic protection that safeguard their connection from surveillance, interception, and impersonation. The V3 protocol represents a major security upgrade over the deprecated 16-character V2 format, incorporating stronger key sizes and improved resistance to directory-based attacks.

Onion Routing
When you access a Torzon Market mirror through Tor Browser, your connection is encrypted in multiple layers and routed through at least three independent relay nodes before reaching the destination server. Each relay peels away one encryption layer to learn only the next hop in the circuit, never the full path. The entry guard knows your IP but not your destination; the exit node knows the destination but not your IP. This layered architecture, resembling the concentric layers of an onion, makes traffic analysis prohibitively difficult for any single observer monitoring the network.
V3 Protocol
Version 3 onion addresses are derived from ED25519 public keys, producing 56-character base32-encoded strings that serve as both the address and a cryptographic fingerprint of the server. This means the address itself authenticates the server you connect to without relying on external certificate authorities or DNS infrastructure that could be compromised. V3 addresses also incorporate improved hidden service directory protocols that prevent relay operators from discovering which onion services their nodes are helping to serve, adding another privacy layer to the mirror network.
Connection Security
Every connection to a V3 onion address is end-to-end encrypted between your Tor Browser and the destination server. Unlike clearnet HTTPS where certificate authorities can be coerced into issuing fraudulent certificates, onion service authentication is inherently trustless because it relies on the mathematical relationship between the address and the server's private key. No third party can intercept, modify, or impersonate the connection as long as you are using the correct 56-character address. This is why character-by-character URL verification against this mirror directory is the most effective defense against phishing attacks.
Torzon Market Anti-Phishing Protection Guide
Phishing remains the dominant attack vector in the darknet ecosystem. Sophisticated operators spend significant resources creating pixel-perfect clones of popular markets, then distribute links through forums, direct messages, and even paid placements on clearnet search engines. Recognizing these threats before you enter any credentials is needed to protecting your account, cryptocurrency, and personal security. The strategies below cover the most common phishing tactics and practical countermeasures every Torzon user should practice consistently.

URL Verification
Always obtain mirror addresses exclusively from this official portal or from the Dread superlist verified by community moderators. Never click onion links found in forum posts, private messages, Telegram groups, or clearnet search results. Phishing operators register thousands of look-alike onion addresses with subtle character substitutions designed to pass casual inspection. Before every login session, copy the full mirror URL from this directory and paste it directly into Tor Browser. Compare the address bar character by character against your saved bookmark to confirm authenticity.
Login Page Inspection
Authentic Torzon login pages include specific security elements that phishing clones frequently omit or implement incorrectly. Check for the presence of a functional CAPTCHA challenge, consistent branding that matches previous visits, and correct page structure including all navigation elements. Phishing sites often simplify the login flow to capture credentials as quickly as possible, removing features like the CAPTCHA, two-factor authentication prompt, or PGP login option. If the login page appears different from what you remember, do not enter your username or password.
Check the section below for more on this topic.
Bookmark Official Sources
Create dedicated bookmarks in Tor Browser for this mirror portal and for two or three individual mirror addresses verified through PGP signatures. Using bookmarks eliminates the need to search for links each session, removing the primary opportunity for phishing operators to intercept your access. Store backup copies of verified mirror URLs in an encrypted KeePassXC database alongside your account credentials. This practice ensures you always have access to authenticated endpoints even if this portal experiences temporary downtime.
Torzon: Security Resources & Tools
Maintaining proper operational security requires the right tools configured correctly. The resources below are trusted, open-source projects recommended by the privacy and security community for safe darknet access. Always download software exclusively from official project websites to avoid tampered distributions.
Privacy Tools
Tor Project - Official Tor Browser for anonymous browsing
Tails OS - Amnesic live operating system
Whonix - Tor-focused anonymity OS
EFF - Digital rights and privacy organization
Access Torzon Market Through Verified Mirrors
Connect securely to Torzon Market using the PGP-authenticated onion addresses listed above. Every mirror in this directory has been verified against the official signing key and is monitored around the clock for availability. Open Tor Browser, paste a verified mirror address, and access the platform with confidence that you are connecting to an authentic endpoint protected by the strongest cryptographic authentication available on the Tor network.
Access Primary Mirror